Cyber Attack Advice
Here are a few ways to try and stop any Ransomware Attack on Your PC:
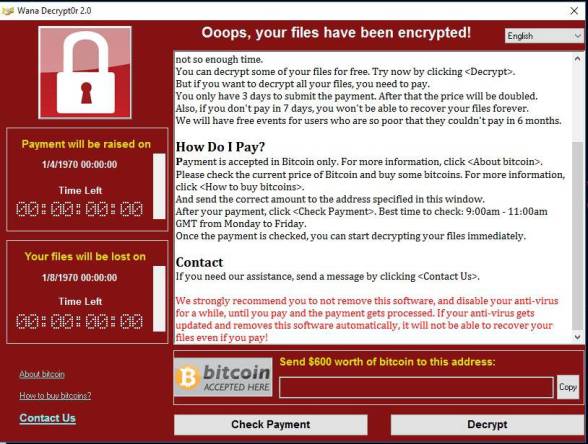
None of us wants to see the screen above, therefore:
1. Install an up to date Operating System.
2. Ensure that your Operating System is always fully updated as patches are released.
3. Install good Anti Virus and Anti Malware and keep these up to date.
4. Make regular manual backups of all important data, documents and photographs. The completed backup should not be connected to your PC or Network.
5. Make sure your Firewall is on and working.
6. Be very careful about which e-mails you open and be wary of attatchments and links in suspect mails.
In our opinion the best way to protect your PC from these attacks is to make regular backups on devices (Flash Drives or External Hard Drives) that are NOT connected to your PC. By keeping your backups disconnected from the PC the Virus / Ransomware cannot spread to the backup device which can then be used to restore your data to your PC once it has been cleaned and after a fresh load of the operating system.
At the present time we believe that defences against these types of attack are at best poor and unreliable and for this reason we recommend regular backups to external unconnected devices. Here we take backups of our PC's to an external hard drive on a weekly basis. We have two hard drives that we rotate in case of failure of one of these. One is kept offsite, with the data encrypted. It may appear that this method is time consuming, however, it is the only reliable defence we know of at the present time.
Please do not rely on cloud backups as if the cloud files on your PC are infected the changes may be uploaded to your cloud based files on syncronisation.